How to Identify and Remove Rogue DHCP Servers from Your Network
Network administrators face numerous challenges in maintaining a secure and stable infrastructure, but few are as insidious as rogue DHCP servers. These unauthorized servers can wreak havoc on your network, causing connectivity issues, security breaches, and hours of troubleshooting headaches. Whether introduced maliciously by an attacker or accidentally by a well-meaning employee who plugged in their home router, rogue DHCP servers represent a serious threat that demands immediate attention.
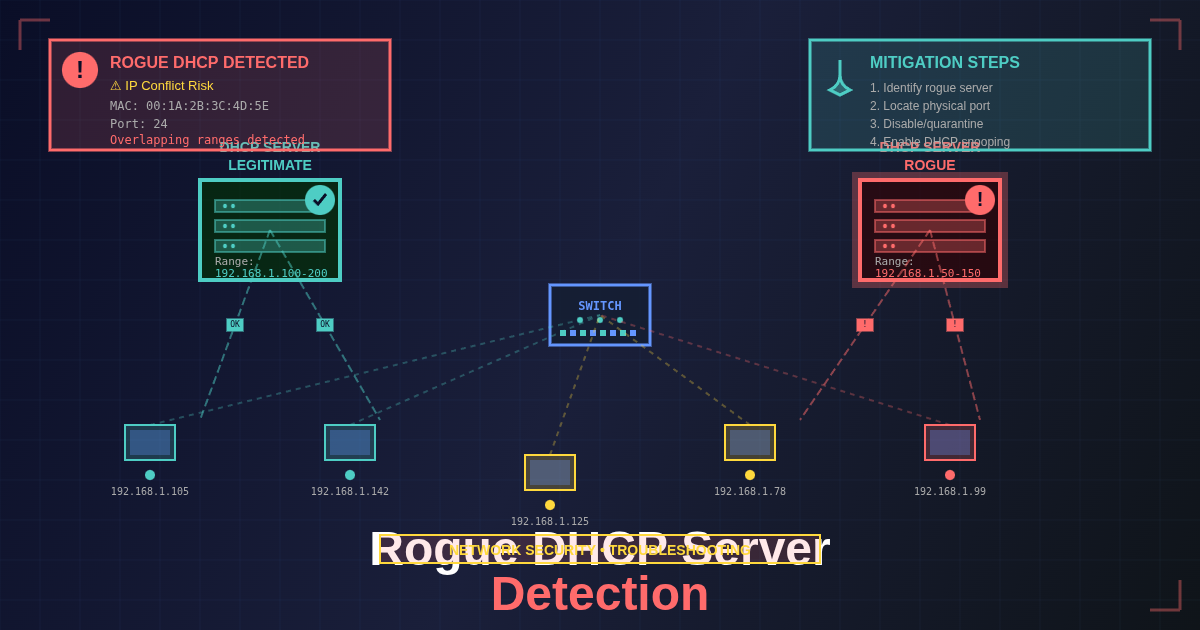
The Dynamic Host Configuration Protocol (DHCP) is fundamental to modern networking, automatically assigning IP addresses and network configuration to devices. When a rogue DHCP server enters your network, it competes with your legitimate server to answer DHCP requests. This creates a race condition where some devices receive correct configuration while others get incorrect settings, leading to intermittent connectivity problems that can be extremely difficult to diagnose. In worst-case scenarios, attackers can use rogue DHCP servers to redirect traffic through compromised systems, enabling man-in-the-middle attacks and data exfiltration.
Understanding how to quickly identify and eliminate rogue DHCP servers is an essential skill for network administrators, system administrators, and security professionals. This comprehensive guide will walk you through the detection process using both passive monitoring and active scanning techniques, provide you with the tools and commands you need, and show you how to permanently secure your network against this threat. You’ll learn professional-grade techniques used in enterprise environments, along with practical strategies you can implement immediately regardless of your network’s size or complexity.
Prerequisites
Before diving into rogue DHCP server detection and removal, ensure you have the following requirements in place:
Technical Knowledge:
- Basic understanding of networking concepts (TCP/IP, subnets, DHCP)
- Familiarity with command-line interfaces (Linux terminal or Windows Command Prompt)
- Understanding of network security principles
Tools and Access:
- Administrative access to your network infrastructure
- Root or sudo privileges on a Linux system (for detection tools)
- Access to network switches and their management interfaces
- Physical access to network equipment (for emergency scenarios)
Software Requirements:
- Linux system with
nmapinstalled (version 7.0 or higher recommended) - Network monitoring tools like
tcpdumpor Wireshark (optional but helpful) - SSH client for remote server management
- Text editor for configuration files
Network Information:
- Your network’s IP address range and subnet mask
- Location of legitimate DHCP server(s)
- MAC addresses of authorized DHCP servers
- Network topology documentation
💡 Tip: If you don’t have a dedicated Linux system for network administration, consider setting up a virtual machine or using a live USB distribution like Kali Linux or Ubuntu. These provide all the necessary tools without requiring permanent installation.
Understanding Rogue DHCP Servers
A rogue DHCP server is any DHCP server operating on your network without authorization. These servers respond to DHCP discovery broadcasts from client devices, potentially providing incorrect network configuration that can disrupt connectivity or compromise security.
How DHCP Works
The DHCP process follows a four-step handshake known as DORA:
- Discovery: Client broadcasts a DHCP discover message
- Offer: DHCP server(s) respond with configuration offers
- Request: Client selects an offer and requests that configuration
- Acknowledgment: Selected server confirms the lease
The critical vulnerability lies in step two: any DHCP server on the network can respond to discovery messages. If multiple servers respond, the client typically accepts the first offer it receives, creating a race condition that rogue servers can exploit.
Common Sources of Rogue DHCP Servers
Accidental Introduction:
- Employee-owned wireless routers or access points with DHCP enabled
- Home networking equipment mistakenly connected to corporate networks
- Virtual machines configured with bridged networking and DHCP services
- Network equipment with factory default settings that include DHCP
Malicious Introduction:
- Attackers deploying rogue servers for man-in-the-middle attacks
- Compromised systems reconfigured to provide DHCP services
- Wireless evil twin attacks with malicious DHCP configuration
- Insider threats attempting to disrupt network operations
💡 Tip: In my experience managing enterprise networks, over 80% of rogue DHCP servers are introduced accidentally. Regular security awareness training significantly reduces these incidents.
Detecting Rogue DHCP Servers with Nmap
Nmap (Network Mapper) provides a powerful and reliable method for detecting DHCP servers on your network through its DHCP discovery script. This active scanning approach simulates a client requesting DHCP configuration and records all responses.
Basic Detection Command
The fundamental command for DHCP server detection is:
sudo nmap --script broadcast-dhcp-discover
This command broadcasts a DHCP discovery request and displays all servers that respond. You must run this with sudo or root privileges because the script requires raw network socket access to craft and send DHCP packets.
Understanding the Output
When you run the detection command, nmap will display results similar to this:
Pre-scan script results:
| broadcast-dhcp-discover:
| Response 1 of 2:
| IP Offered: 192.168.1.100
| DHCP Message Type: DHCPOFFER
| Server Identifier: 192.168.1.1
| Router: 192.168.1.1
| Subnet Mask: 255.255.255.0
| Domain Name Server: 8.8.8.8, 8.8.4.4
| Response 2 of 2:
| IP Offered: 192.168.1.150
| DHCP Message Type: DHCPOFFER
| Server Identifier: 192.168.1.50
| Router: 192.168.1.50
| Subnet Mask: 255.255.255.0
Key Information to Extract:
- Number of responses: More than one response typically indicates a rogue server
- Server Identifier: The IP address of each responding DHCP server
- Router/Gateway: Shows what gateway the server is advertising (potential indicator of malicious configuration)
- DNS Servers: Rogue servers often advertise attacker-controlled DNS servers
- IP Offered: The address being offered to the client
Advanced Detection Options
Specifying Network Interface:
If your system has multiple network interfaces, specify which one to use:
sudo nmap --script broadcast-dhcp-discover -e eth0
This ensures the DHCP discovery broadcast goes out on the correct network segment.
Multiple Detection Attempts:
For more reliable detection, especially on busy networks, run multiple scans:
for i in {1..5}; do sudo nmap --script broadcast-dhcp-discover; sleep 2; done
This runs five consecutive scans with two-second intervals, helping identify intermittent rogue servers that might not respond to every request.
Detailed Output with Debugging:
For troubleshooting or detailed analysis:
sudo nmap --script broadcast-dhcp-discover -d
The -d flag enables debugging output, showing exactly what packets are being sent and received.
💡 Tip: Run detection scans during different times of day. Some rogue servers (particularly those on employee equipment) may only be active during business hours.
Identifying the Physical Location
Once you’ve detected a rogue DHCP server, your next critical task is locating the physical device. The MAC address provides the key to tracking down the hardware.
Extracting MAC Address Information
Use nmap with MAC address resolution:
sudo nmap -sP 192.168.1.50 | grep "MAC Address"
Replace 192.168.1.50 with your rogue server’s IP address. This returns output like:
MAC Address: 00:11:22:33:44:55 (Cisco Systems)
The manufacturer information (Organizationally Unique Identifier or OUI) provides valuable clues about the device type.
Using Network Switch Port Mapping
Most managed network switches maintain MAC address tables that show which MAC addresses are learned on which physical ports:
Cisco IOS:
show mac address-table address 0011.2233.4455
HP ProCurve:
show mac-address 00:11:22:33:44:55
Dell/Force10:
show mac-address-table address 0011.2233.4455
The output reveals the switch port number where the device is connected, allowing you to trace the physical cable to the device’s location.
Using LLDP or CDP for Device Discovery
Link Layer Discovery Protocol (LLDP) and Cisco Discovery Protocol (CDP) can provide additional information about connected devices:
sudo lldpctl
Or on Cisco switches:
show cdp neighbors detail
These protocols can reveal device hostnames, system descriptions, and management IP addresses, making identification easier.
💡 Tip: Create a network topology diagram with switch port mappings during your initial network setup. This dramatically reduces the time required to locate rogue devices from hours to minutes.
Removing the Rogue DHCP Server
After identifying and locating the rogue server, you need to remove it quickly while minimizing network disruption.
Immediate Mitigation Steps
1. Disable the Switch Port:
The fastest method to stop a rogue DHCP server is disabling the network switch port it’s connected to:
# Cisco IOS
interface GigabitEthernet1/0/24
shutdown
This immediately disconnects the device without requiring physical access.
2. Physical Disconnection:
If you have immediate physical access, simply unplug the network cable. This is the most foolproof method but isn’t always practical in large or remote environments.
3. Block via MAC Address Filtering:
Configure your switches to block the rogue server’s MAC address:
# Cisco IOS
mac access-list extended BLOCK-ROGUE
deny host 0011.2233.4455 any
permit any any
interface range GigabitEthernet1/0/1-48
mac access-group BLOCK-ROGUE in
Device Investigation and Remediation
Once you’ve isolated the device, investigate why it was acting as a DHCP server:
For Accidental Rogue Servers:
- Disable DHCP services on the device
- Configure it as a DHCP client instead
- Document the incident for user training
- Update security policies if needed
For Suspected Malicious Servers:
- Preserve the device for forensic analysis
- Do not power it off immediately (volatile memory contains evidence)
- Contact your security team or incident response provider
- Review logs for signs of compromise on other systems
- Scan the network for additional compromised devices
Verification After Removal
Confirm the rogue server is eliminated:
# Run detection scan again
sudo nmap --script broadcast-dhcp-discover
# Should now show only legitimate server(s)
Check for any lingering issues on client devices:
# Windows
ipconfig /release
ipconfig /renew
# Linux
sudo dhclient -r
sudo dhclient
Best Practices for DHCP Security
Implementing comprehensive DHCP security measures prevents rogue servers from causing problems in the first place.
1. Enable DHCP Snooping on Network Switches
DHCP snooping is a Layer 2 security feature that validates DHCP messages and builds a binding table of legitimate DHCP assignments. Configure it on all access switches:
# Cisco IOS example
ip dhcp snooping
ip dhcp snooping vlan 10,20,30
interface GigabitEthernet1/0/1
ip dhcp snooping trust
interface range GigabitEthernet1/0/2-48
ip dhcp snooping limit rate 10
Mark only your legitimate DHCP server ports as trusted, while limiting DHCP packet rates on untrusted ports to prevent DoS attacks.
2. Implement Port Security with MAC Address Limits
Restrict the number of MAC addresses allowed per switch port and configure violation actions:
interface range GigabitEthernet1/0/2-48
switchport port-security
switchport port-security maximum 3
switchport port-security violation shutdown
This automatically disables ports that violate security policies, including those with rogue DHCP servers.
3. Deploy Network Access Control (NAC)
NAC solutions like Cisco ISE, Aruba ClearPass, or PacketFence verify device compliance before granting network access. These systems can automatically detect and quarantine devices running unauthorized services including DHCP servers.
4. Regular Automated Scanning
Schedule automated rogue DHCP detection using cron jobs:
# Add to crontab
0 */6 * * * /usr/local/bin/dhcp-scanner.sh >> /var/log/dhcp-scan.log 2>&1
Create a simple scanning script that emails alerts when multiple DHCP servers are detected, enabling rapid response even outside business hours.
5. Network Segmentation and VLANs
Segment your network into VLANs based on trust levels and function. This limits the scope of damage a rogue DHCP server can cause:
- Management VLAN (highly restricted)
- Server VLAN (controlled access)
- User VLAN (regular employee devices)
- Guest VLAN (isolated from internal resources)
- IoT VLAN (isolated smart devices)
6. Comprehensive Documentation
Maintain detailed records of authorized DHCP servers including:
- IP addresses and hostnames
- MAC addresses
- Switch ports they’re connected to
- Administrative contacts
- Configuration details
This documentation enables rapid verification when investigating potential rogue servers.
7. Security Awareness Training
Educate users about the risks of connecting unauthorized networking equipment. Many rogue DHCP incidents stem from employees innocently connecting personal devices to corporate networks.
Common Pitfalls and How to Avoid Them
Understanding frequent mistakes helps you navigate rogue DHCP detection and removal more effectively.
Pitfall 1: False Positives from Legitimate Redundant DHCP Servers
Many enterprise networks intentionally run multiple DHCP servers for redundancy and failover. These legitimate servers appear as “multiple responses” during detection.
Solution: Maintain an accurate inventory of authorized DHCP servers. Configure your detection scripts to alert only when unknown servers appear. Use DHCP server identifiers to distinguish between authorized and rogue servers in automated monitoring.
Pitfall 2: Racing to Disable Ports Without Investigation
Immediately shutting down a switch port might disconnect critical infrastructure. In one incident I encountered, what appeared to be a rogue DHCP server was actually a backup server that had been activated during maintenance.
Solution: Always verify the device identity before taking action. Check with your team whether any maintenance or changes are in progress. Document your findings before executing mitigation steps.
Pitfall 3: Overlooking Virtual Machine DHCP Services
Virtualization platforms like VMware, VirtualBox, and Hyper-V often include built-in DHCP services for virtual networks. When virtual machines are configured with bridged networking, these services can leak onto the production network.
Solution: Audit virtualization hosts regularly. Configure virtual networks to use NAT instead of bridged mode when possible. Implement network policies that detect and alert on traffic from virtualization management interfaces.
Pitfall 4: Failing to Check All Network Segments
Large networks with multiple switches and VLANs require comprehensive scanning. A single scan from one location might miss rogue servers on different network segments.
Solution: Deploy scanning hosts in each network segment or VLAN. Alternatively, use network traffic mirroring (SPAN/mirror ports) to aggregate traffic for centralized monitoring. Document your network topology to ensure complete coverage.
Pitfall 5: Neglecting Wireless Networks
Rogue DHCP servers on wireless networks pose particular challenges because the devices may be mobile or only intermittently connected. Wireless evil twin attacks often include rogue DHCP services.
Solution: Implement wireless intrusion detection systems (WIDS) that monitor for rogue DHCP servers. Configure wireless controllers to detect and automatically contain rogue access points. Regularly audit wireless networks separately from wired infrastructure.
Real-World Use Cases
Use Case 1: Home Router Causing Corporate Network Outage
A financial services company experienced intermittent connectivity issues affecting approximately 40% of devices on one floor. Users reported being unable to access internal resources, while internet connectivity worked normally. Investigation revealed an employee had connected a personal wireless router to provide better WiFi coverage in their area. The router’s DHCP server was issuing addresses with the router itself as the gateway, creating a black hole for internal traffic.
Resolution: Network administrators used nmap to identify two responding DHCP servers. The MAC address of the rogue server indicated a consumer-grade TP-Link router. Switch port mapping traced it to a cube in the accounting department. The device was removed, DHCP snooping was enabled across all access switches, and the company implemented a policy requiring IT approval for all network devices.
Use Case 2: Compromised Server in Man-in-the-Middle Attack
A healthcare organization detected unusual DNS queries to unknown domains during routine security monitoring. Further investigation revealed that some workstations were receiving DHCP configuration pointing to attacker-controlled DNS servers. The rogue DHCP server was actually a compromised Linux server in the data center that attackers had reconfigured after exploiting an unpatched vulnerability.
Resolution: The security team immediately isolated the compromised server using ACLs while preserving it for forensic analysis. They deployed emergency detection scripts across all network segments to identify any other compromised systems. Post-incident review led to implementation of network segmentation, enhanced patch management, and deployment of a NAC solution requiring health checks before network access.
Use Case 3: Testing Lab Affecting Production Network
A technology company’s development team set up a testing environment to simulate customer networks. They configured multiple DHCP servers to test various scenarios but accidentally connected the testing equipment to the production network through a misconfigured switch port. Production devices began receiving test IP addresses in the wrong subnet, causing widespread connectivity failures.
Resolution: Network operations identified the issue within 15 minutes using automated monitoring that detected abnormal DHCP response patterns. They immediately disabled the misconfigured switch port and implemented additional VLAN controls to ensure physical separation between testing and production environments. The incident prompted review of change management procedures for network modifications.
Performance Considerations
DHCP detection and security measures can impact network performance and operations if not implemented thoughtfully.
Detection Scan Impact
Active DHCP discovery scanning generates broadcast traffic that, while minimal for occasional scans, can accumulate during continuous monitoring:
- Single nmap scan: Generates approximately 5-10 packets
- Continuous monitoring: Schedule scans no more frequently than every 15-30 minutes
- Large networks: Distribute scanning across multiple systems to avoid bandwidth concentration
💡 Tip: During initial deployment, run intensive scanning for 24-48 hours to establish baseline behavior, then reduce frequency to every 2-4 hours for ongoing monitoring.
DHCP Snooping Overhead
DHCP snooping requires switches to inspect and validate every DHCP packet, introducing minimal latency (typically less than 1ms) but consuming switch CPU resources:
- Enable incrementally: Deploy DHCP snooping on one switch or VLAN at a time while monitoring CPU utilization
- Rate limiting: Configure appropriate DHCP rate limits (typically 10-15 packets per second for access ports)
- Trusted port placement: Carefully designate trusted ports to minimize unnecessary inspection
Storage Requirements for Logging
Comprehensive DHCP monitoring generates logs that accumulate over time:
- Estimated log volume: 1-5 MB per day per 100 devices
- Retention recommendations: Maintain 90 days of logs for investigation and compliance
- Log rotation: Implement automated log rotation and compression to manage storage
Testing Your Implementation
Validating your rogue DHCP detection and prevention measures ensures they’ll work when needed.
Creating a Controlled Test Environment
Never test with actual rogue servers on production networks. Instead, create an isolated testing environment:
- Set up a test VLAN or separate network segment
- Deploy a test DHCP server (can use a Linux VM with
dnsmasqor a spare router) - Connect test clients to verify detection without affecting production
Detection Testing Procedure
Step 1: Run baseline detection scan in your test environment:
sudo nmap --script broadcast-dhcp-discover -e eth1
Verify it detects only your legitimate test DHCP server.
Step 2: Introduce your test rogue DHCP server on the same network segment.
Step 3: Run detection again and confirm both servers appear in results.
Step 4: Verify automated monitoring alerts trigger correctly (if implemented).
DHCP Snooping Testing
After enabling DHCP snooping in your test environment:
Test 1 - Legitimate Server: Connect a test client to a switch port with an untrusted configuration. Verify the client receives DHCP configuration from the trusted legitimate server.
Test 2 - Rogue Server Prevention: Connect your test rogue server to an untrusted port. Attempt to offer DHCP addresses. Verify the switch blocks DHCP offers from untrusted ports.
Test 3 - Violation Actions: Configure violation action to shutdown and verify the port disables automatically when violations occur.
Port Security Testing
Verify port security prevents MAC address spoofing and limits device counts:
# Generate test traffic with different MAC addresses
# Port should shut down after exceeding configured maximum
Documentation of Test Results
Record all test outcomes including:
- Detection accuracy and timing
- False positive rates
- Alert generation and delivery
- Mitigation effectiveness
- Recovery procedures
Regular testing (quarterly recommended) ensures your defenses remain effective as your network evolves.
Conclusion
Rogue DHCP servers represent a serious threat to network stability and security, but with proper detection tools and preventive measures, you can effectively protect your infrastructure. The key takeaways from this guide include:
1. Detection is Critical: Regular scanning using tools like nmap’s broadcast-dhcp-discover script enables rapid identification of unauthorized DHCP servers before they cause significant damage. Implement automated monitoring to catch rogue servers immediately rather than waiting for user complaints.
2. Layer Your Defenses: Don’t rely on a single security measure. Combine DHCP snooping, port security, network segmentation, and regular monitoring to create comprehensive protection. Each layer catches threats that others might miss.
3. Speed Matters in Response: The faster you identify and isolate a rogue DHCP server, the less impact it has on your network. Maintain updated documentation of authorized servers and established procedures for rapid mitigation, enabling your team to respond within minutes rather than hours.
4. Most Incidents Are Accidental: While maintaining vigilance for malicious attacks, remember that the majority of rogue DHCP servers result from innocent mistakes. Security awareness training and clear policies dramatically reduce accidental incidents.
5. Test and Validate: Your detection and prevention measures are only effective if they actually work. Regular testing in controlled environments ensures your defenses remain functional and your team knows how to respond when real incidents occur.
By implementing the techniques, tools, and best practices outlined in this guide, you’ll be well-equipped to maintain a secure, stable network environment free from the disruptions caused by rogue DHCP servers. Remember that network security is an ongoing process requiring continuous monitoring, regular testing, and staying informed about emerging threats and detection techniques.
Additional Resources
Expand your knowledge and capabilities with these valuable resources:
- Nmap Official Documentation - DHCP Scripts: https://nmap.org/nsedoc/scripts/broadcast-dhcp-discover.html - Comprehensive reference for nmap’s DHCP discovery capabilities and advanced options
- RFC 2131 - Dynamic Host Configuration Protocol: https://www.rfc-editor.org/rfc/rfc2131.html - The official DHCP protocol specification, essential for understanding DHCP fundamentals
- DHCP Snooping Configuration Guide (Cisco): https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/15-0SY/configuration/guide/15_0_sy_swcg/dhcp_snooping.html - Detailed implementation guide for DHCP snooping on Cisco switches
- SANS Institute - Securing DHCP Services: https://www.sans.org/reading-room/whitepapers/networkdevs/securing-dhcp-services-1547 - Comprehensive whitepaper covering DHCP security architecture and best practices
- Wireshark DHCP Filter Reference: https://wiki.wireshark.org/DHCP - Learn to analyze DHCP traffic in detail using Wireshark for advanced troubleshooting
- Network Access Control Deployment Guide: https://www.cisco.com/c/en/us/solutions/enterprise-networks/network-access-control-nac/index.html - Overview of NAC solutions for preventing rogue devices
- DHCP Best Practices - Microsoft Docs: https://docs.microsoft.com/en-us/windows-server/networking/technologies/dhcp/dhcp-top - Best practices for Windows-based DHCP infrastructure, including redundancy and security configurations
